Keeping the subject in focus and making the background blur can make your dull photographs exciting and appealing. But how to perform this task on your android and iOS gadgets?
Well, Blur Background apps offer the ultimate solution to this issue. In this article, we will discuss some of the best apps to blur the background of your pictures.
We are living in a tech-driven century where clicking stunning pictures using your mobile phones is extremely easy.
Smartphones offer fantastic camera quality, along with several editing tools. Every second day a new tool makes its way to the app store, including the blur background apps.
Many smartphones come with in-built photo editing apps, but some need a dedicated app to add a blur effect to your pictures.
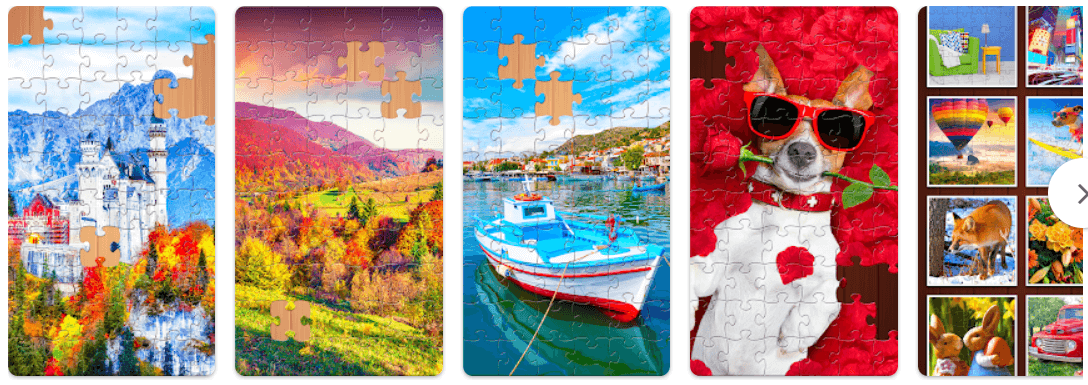
Here is a list of some of the best apps that can blur the background and add life to your boring and dull images. Go through the list of apps to blur background and pick the one that fits in well with your requirements.
Best Blur Background Apps for Android and iPhone in 2024
Adding a blurred background to your pictures without a professional camera seemed impossible in earlier times.
But in the last couple of years, several blur picture apps have been developed that can assist you well in blurring the background of your dull images. These apps offer an excellent way to transform your images and showcase your creativity.
1. Square Pic- Photo Editor, Blur Image Background
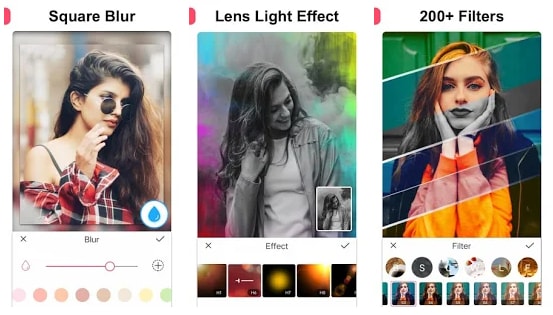
Editing photos and making blur backgrounds is easy with the Square Pic app. The user can easily change the image the way they want with its amazing features. Using the app user can adjust the blur strength, add effects, filters and stickers.
The interface which the app offers is really simple, any user can edit and add effects to the image. All you need to do is select the image to import and add filters or effects from the list. That’s it you have changed your image successfully.
Must Read: Best Free Passport Size Photo Maker
2. Snapseed – Blur Photo Background App
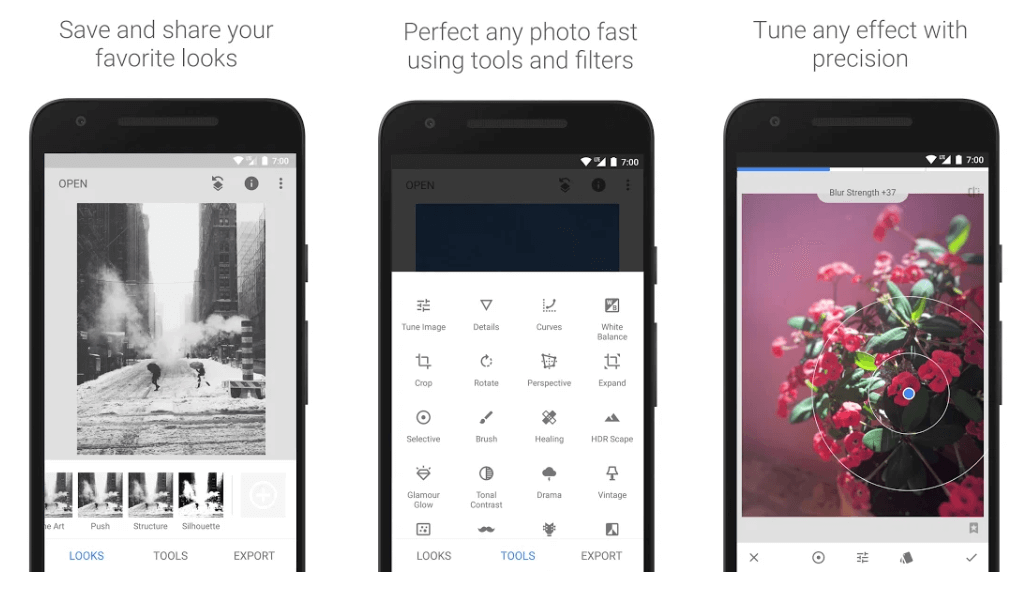
Snapseed is a popular name among smartphone users who love photography. It is a product of Google and offers several picture editing tools.
You can use this Blur photo Background App to bring the main object in focus by adding an out-of-focus background to your images.
Become a self-taught photographer with this stunning app to blur background and add more clarity to your images. Use the below download links to try this app today.
3. After Focus – Blur Picture App

Next in the list of blur picture apps is After Focus. Use it to apply Zoom, motion, and Lens effects to your pictures. You can either choose to take a new picture or edit an existing image from your photo gallery.
It is a stunning app that can effortlessly blur the background of your images with intricate edges.
Must Read: Best Android Camera Apps For Quality Pictures
To select a focus area, draw a boundary, and then choose the type of blur you wish to add. It comes for free. However, if you want an ad-free working, you can choose to use its Pro version at $1.83.
4. Motionleap by Lightricks – Photo Animator
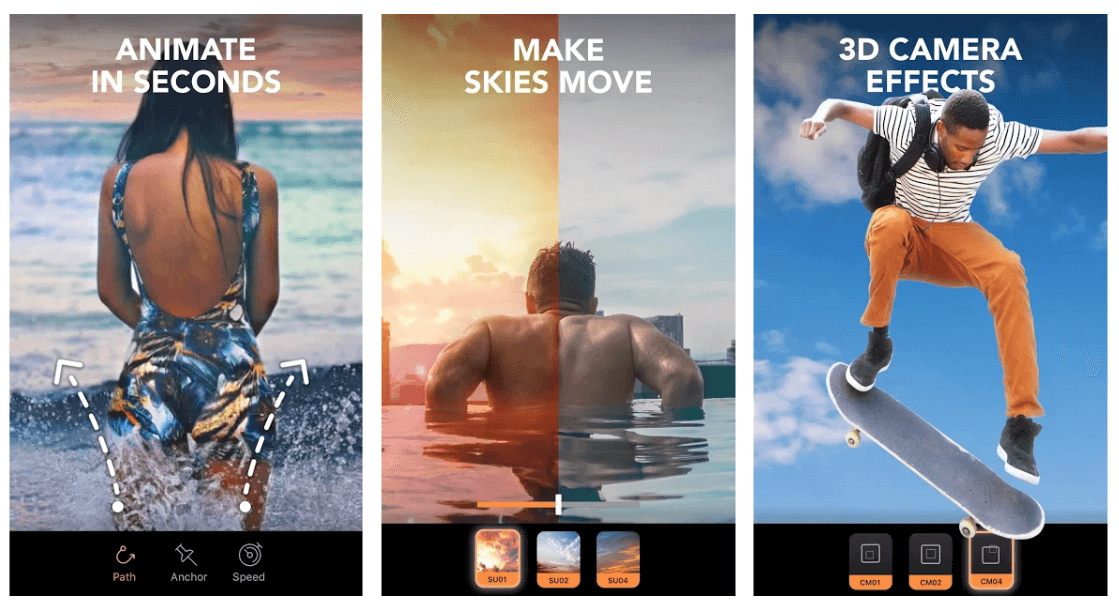
If you are looking for an app with professional-level edits, then Motionleap can be a decent option for you. You can use it to edit, adjust, and animate your boring images. You can use it to edit, adjust, animate your boring images and as blur background app for android.
Motionleap is compatible with both Android and iOS platforms and has several useful editing tools to offer. You can use it to put the main object in focus by adding a blur effect to the background.
Linear, radial, and mirrors are some tilt-shift styles that you can apply to your images using this Blur Background App.
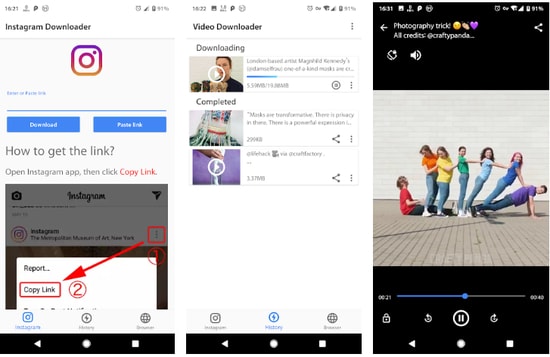
5. Instagram
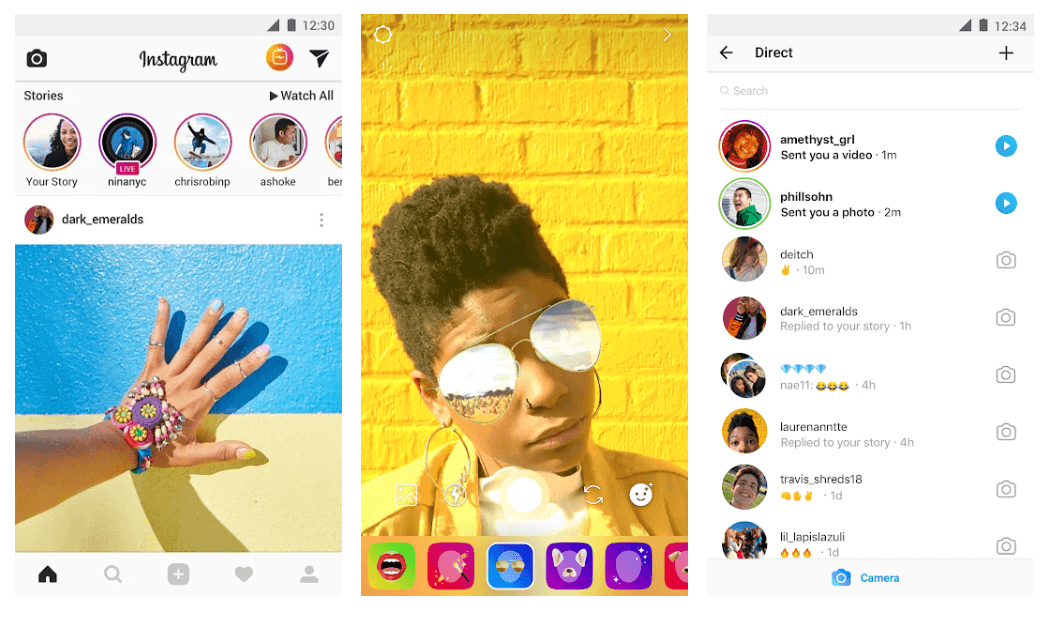
Besides being one of the most loved social media platforms, Instagram also has many stunning image editing tools to offer. Edit your pictures and share them on your profile for your friends to see.
You can add a blurred background and apply a bokeh effect to bring the main object of your picture in focus. Use its Edit section to add a Tilt-shift to your photographs, Radial and linear are the other two options that you may consider.
To download this Blur photo Background App for your smartphones, use the below links.
6. PicsArt Photo Editor
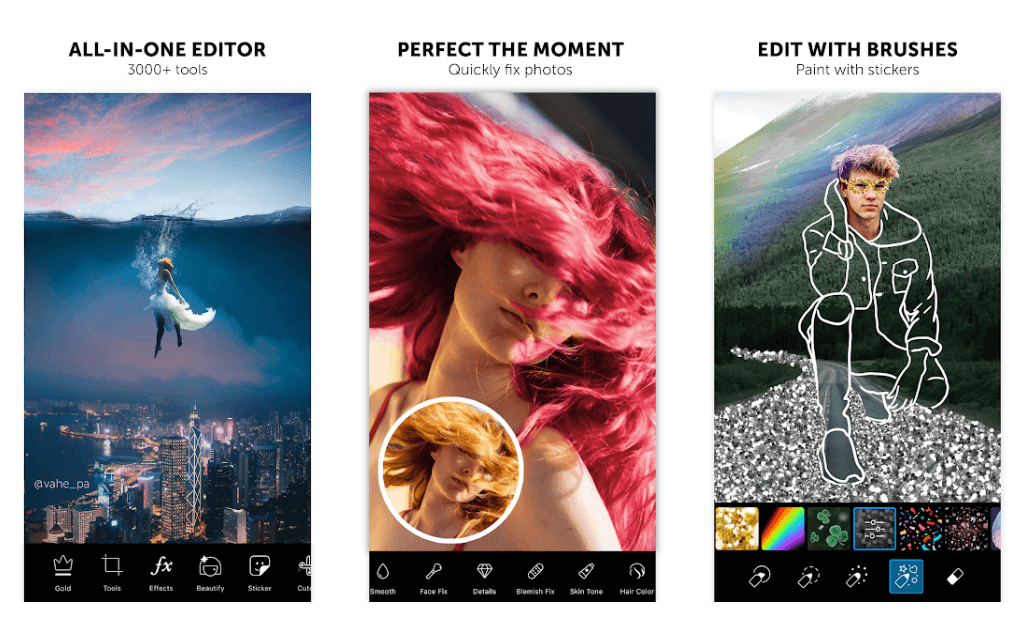
Next one in the list of best app to blur background is Picsart. The Photo Editor application is one of the most popular apps for making the background blur. It enjoys over 500 million satisfied users.
This power-packed app offers a massive basket of stunning features and effects, including Motion, Smart, normal blur, and many more. You can use it to edit, alter, and crop your picture the way you want.
Besides being one of the most efficient apps to blur the background of your images, it can also be used to make custom stickers. It is compatible with both iOS and Android devices and is exceptionally easy to use.
7. Facetune 2 – Selfie Photo Editor
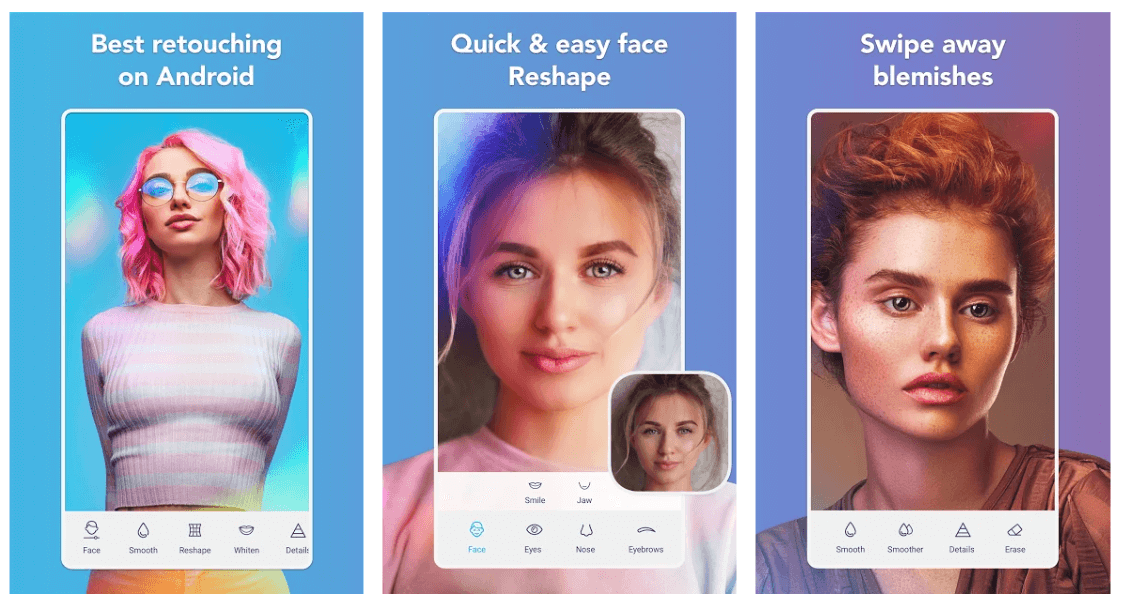
If you are addicted to selfies, then Facetune2 can be the right choice for you. The app provides you with several options to retouch and alter your images by adding a blurred background to them.
Apart from being a trusted app for blurring background, you can also use it to add glitter, makeup filters, and whiten teeth in your selfie pictures. The blur background feature works on a real-time basis, but you can also use it for your existing images.
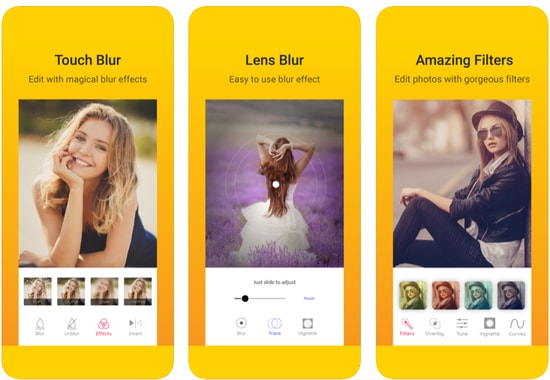
8. Cymera – Best Blur Effect & Filters
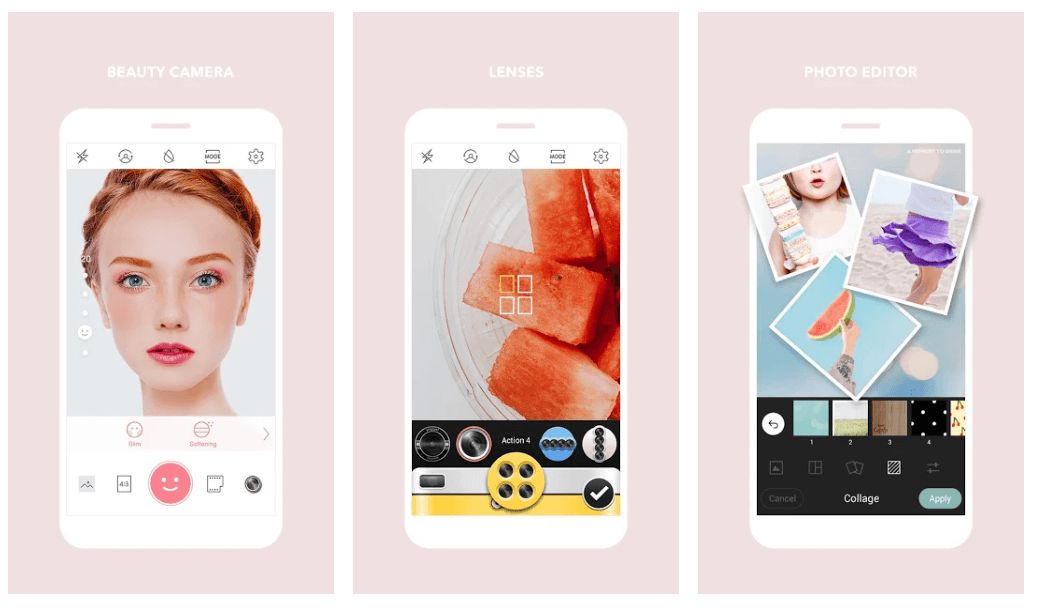
Capture and edit pictures with this feature-rich blur picture application. It has different lenses, which you can choose to take better photos. It also provides multiple blur effects and filters.
Use it to blur the background, adjust the contrast and brightness of your pictures in a fast and secure manner. You can also choose to add some makeup effects to your images with Cymera.
Must Read: Best Photo to Cartoon Picture Apps For Android & iOS
9. Blur Image Background – Blur Background Blur Photo
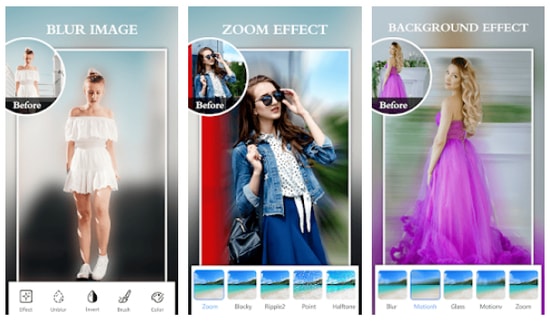
Blur Image Background Editor is another excellent app that blurs background, designed specifically for users who loves to give their favorite photos and selfies a breathtaking look. With the help of this simple to use application, you can effortlessly blur the background of your images or unwanted objects without having to pay a single penny.
However, similar to other blur photo background apps, this application also offers in-app purchases in order to provide access to the highly advanced photo editing tools.
10. Blur Photo & Background
Blur Photo & Background is a fast and easy to use application to blur image background for free. You can effortlessly change the look and feel of your pictures using its amazing blurry effects.
Moreover, this blur picture editor comes with a wide variety of photo editing tools like curve control, color adjustment, and many others to help you turn your beautiful shots into masterpieces. These features are add on to its functionality of the photo app to blur background of your images. You can get this excellent application for free by clicking on the link given below.
11. DSLR Blur Photo
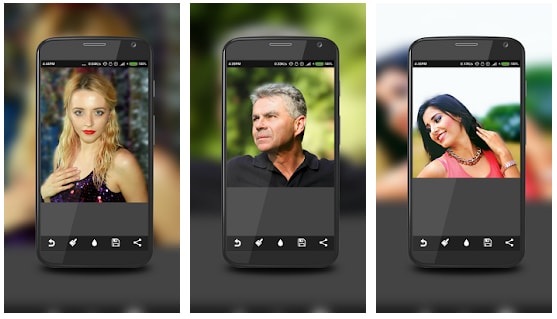
Another one in the list of best background blur apps is DSLR Blur Photo. It is a dedicated app that offers the user to blur their images. The user can blur the images, change the blur strength, and can also select the area where they want the effect to be. The app is very simple to use. Moreover, Android users can enjoy this amazing app for blurring the background pretty easily. While other apps offer many other features this app is dedicated to blurring the background only, which can make you think before installing it. But you can easily create blur images with this app. Android users have rated this app 3.8 out of 5.
App to Blur Background – FAQs
Q1. How can I blur a picture for free?
There are a lot of apps both free and paid available online that allow users to blur their pictures for free. We have mentioned the best blur photo background applications for Android and iOS. Use any of the above-listed apps that fit in well with your requirements.
Q2. How can I blur the background of a photo?
Pick any of the above applications and allow access to your picture. Follow the in-app steps to blur the background. The above list has applications for both Android and iOS users to blur the background for any picture.
Must Read: Best Photo Recovery Apps
Wrapping up – Blur Photo Background Apps
Explore and discover the world of photography with various picture editing apps. Use them to polish your images by adding a blur effect to them.
Do not settle for less when you can add a new life to your dull pictures. Use various blur effects to highlight the subject and add a creative touch to your images.
Refer to our list of some of the best Blur photo Background App and start with your creative journey.



![How to Download Playlist from YouTube Using IDM [Step by Step]](https://wpcontent.techpout.com/techpout/wp-content/uploads/2021/03/26160407/How-to-Download-Playlist-from-Youtube-Using-IDM-Step-by-Step-150x150.jpg)

1 Comment
Blur Background – Blur image app best tool for set the blurry image effect on your photo to using the android phone. Auto blur shapes effect & blur image background easily after using this blur app.