Tailgating in Cyber Security: Complete Guide
In the modern world of cyber security, much of the focus tends to be on digital threats like hacking, malware, and phishing. However, there are also physical security risks that can lead to major breaches in safety and privacy. One […]
Gcore Web Application Security, Pricing and Features
Web applications are necessary for the functioning of companies within the virtual age, serving as gateways for purchaser interactions, records storage, and transactions. As the reliance on those packages grows, so does the need for robust security measures to shield […]
6 Best Nord VPN Alternative You Should Use in 2024
Best alternatives to Nord VPN ensure online safety at a minimum price (some of them are even free) with a fast connection and many features. Hence, you may go through this article to know about them. In the modern world […]
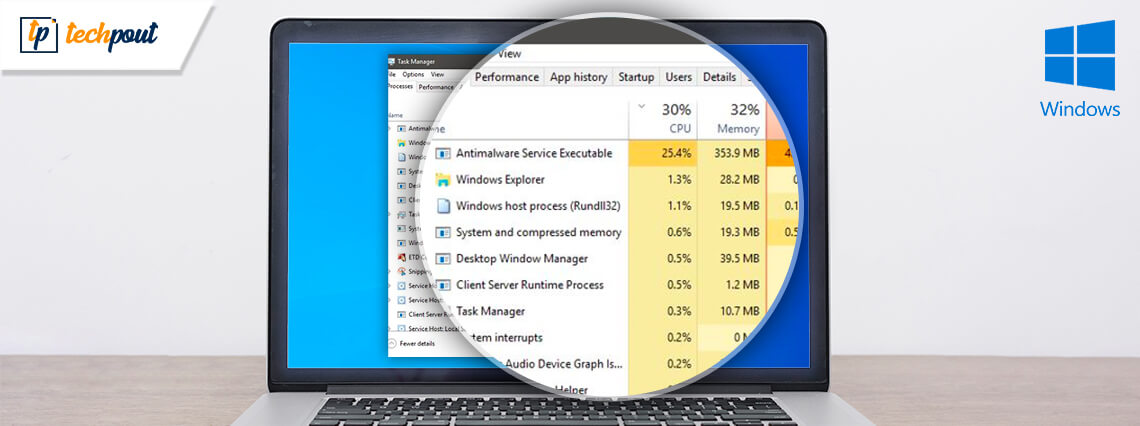
How to Fix ‘Antimalware Service Executable’ High CPU Usage
The Windows security process called Antimalware Service Executable sometimes consumes more than expected resources, degrading the computer’s performance. Hence, you can try the fixes shared in this article to solve the process’s high memory usage problem. A part of Windows […]
How Faiq Farooq is Single-Handedly Upbringing Cybersecurity Industry
Digital attacks are getting more and more common by the day. Digital threats from hackers, ransomware developers, and other security meddlers are becoming a thing to worry about for all. Thankfully, cybersecurity and its practices are there to protect you […]
Is “[email protected]” Legit and How to Prevent this?
Phishing on Instagram has been reported by many users lately. It involves direct messages or emails that look like coming directly from Instagram. As a result of which, your personal information is leaked or your account is lost. Although there’s […]
Difference Between VPN and Proxy Server | Proxy vs VPN
In this article, you will find different points of difference between proxy and VPN to clear the concept, working, and other attributes of the two. You must have heard about proxy servers and VPNs. Both are amazing techniques or tools […]
What is a Network Security Key
Read out the complete article to learn everything you need to know about network security key Windows 10, 11, or older version devices. Are you setting up your WiFi or troubleshooting it and are unable to find your network security […]
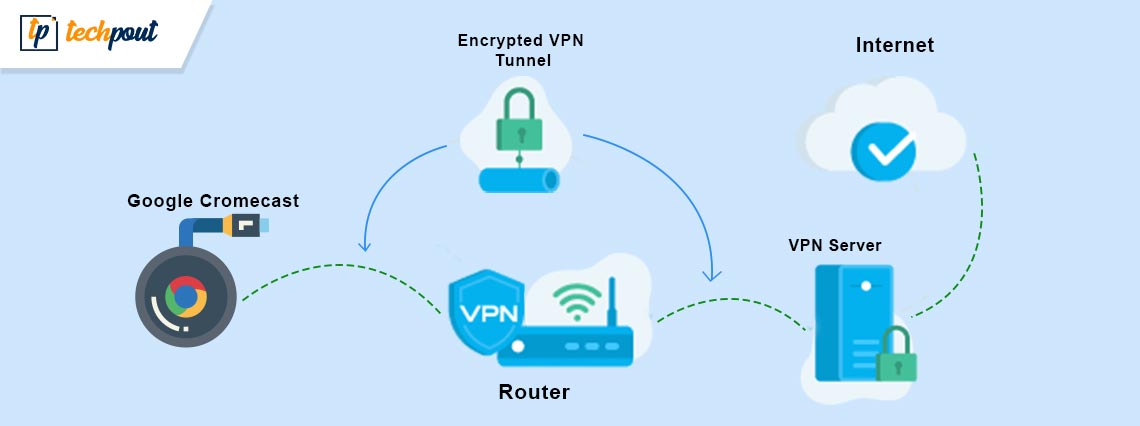
How to Set up VPN on Chromecast
If you want to know how to set up a VPN on Chromecast and surf anonymously, then everything explained in this article will help you do the same with ease. VPN or a Virtual Private Network allows you to connect […]
- 1
- 2