Technology is fast paced. Some of the finest examples are the app and system update notifications you receive on your phones and laptops. No matter which brands you own, all of them tend to keep their apps and OS updated. If they don’t, it does not mean that the tools you use have no flaws. In some cases, the support for specific software gets dropped, or the company no longer invests in its development. However, even if we receive notifications to update, some of us tend to skip these updates.
Though it is good to save some space on your devices by dodging these updates, it may not turn out to be good for you in the end. Why?
As software is the prime element of today’s machines, it may damage the system badly if not updated on time. Vulnerabilities are the loopholes hackers need to compromise devices. For instance, ZDNet had reported that many security gaps hackers exploit had been patched sometime in the past. The main problem is that users do not apply these updates and keep using outdated software. Then, they become potential victims of various threats like ransomware or other malware.
Here are some common software issues that you may face. But don’t worry! We have also included some solutions to these issues. So, read ahead to know more!
Injection Flaws
The number one software issue, or should we say security issue, is the injection flaw. It is an attack where a hacker can take full control of the web app or software by shelling commands, provided the web app takes user input. Thus, the hacker or any other unauthorized user can access the back-end database and add, remove, and even alter information at will.
Even worse, if necessary, the attacker can even change the entire script of the application to make it work the way they want. Some of the common injection flaws are:
- SQL Injection
- HTML Injection
- XML Injection
- LDAP Injection
- OS Command Injection
Here are some ways to prevent injection flaws:
- It is essential to encode the command received and pay special attention to some characters as they are the elements that are exploited by the hackers.
- Input validation. Add an input validation mechanism in your software to ensure that inputs are in the correct format.
Also Read: 13 Best Free Malware Removal Tools for Windows PC in 2021
Cross-Site Scripting
This security vulnerability allows cybercriminals to compromise the data and interactions between the users and the target website or software.
In this attack, hackers tend to manipulate the target website so that it returns harmful JavaScript to the users. When running on the user device, this script compromises their interaction with the website, and hackers can access all the interactions that users make with the website. They can even act as legitimate users to gain access to their personal data like passwords.
There are three major types of XSS attacks, namely,
- DOM-based XSS
- Stored XSS
- Reflected XSS
Here are some ways to prevent XSS attacks:
- Leverage response headers. One of the ways to counteract XSS attacks is to use specific headers in the HTTP responses. It will help in testing if the responses are correct or not.
- Filter the input and encode it. The evergreen way to prevent the XSS attack is to filter the input w.r.t what is valid. Moreover, encode the input to prevent it from looking like active content.
Also Read: Best Ways to Fix ‘Bad System Config Info’ Error in Windows 10
Insufficient Logging and Monitoring
Insufficient logging and monitoring deal with scenarios where the security-critical events of the system are not logged off properly. The occurrence of these incidents affects the health of the system and the incident handling process.
As log monitoring is necessary for securing and preventing a data breach, they need to be given the utmost priority to ensure security. Here are some ways to prevent insufficient logging and monitoring:
- Ensure that all of your sensitive actions on the system software are logged, like logins, transactions, and changes in credentials, if any. These will be helpful in the investigation later.
- Make sure that all of your logs are synced and backed up. Even if the hacker clears your logs, you will have the backup secure.
Also Read: The Default Gateway is Not Available on Windows 10 {Solved}
What Does this Mean for You?
For the most, users are not interested in the classification of vulnerabilities. However, learning what certain flaws can lead to is essential. For instance, if the tool you use contains a vulnerability allowing anyone to read your chats, it is a major problem. It is common for users to neglect the updates due to several reasons. They might see the update as an inconvenience, or they might fear that it will change/remove some of the functionality they like.
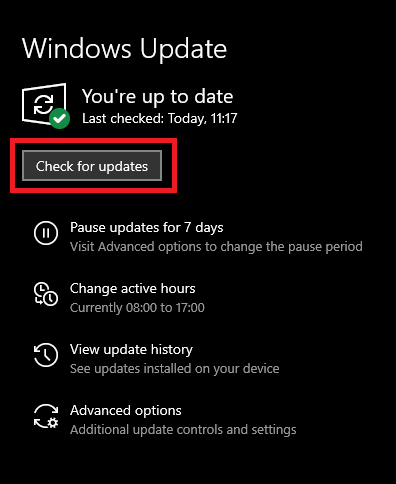
In any case, updates are essential, and you should always ensure that your apps and OS run the latest version.
Final Words
To conclude, we can say that cyberattacks are not to be taken lightly. They can cause severe damage to your device and files. In some cases, vulnerabilities are the main cause of these incidents. What should you do? Here is a quick rundown:
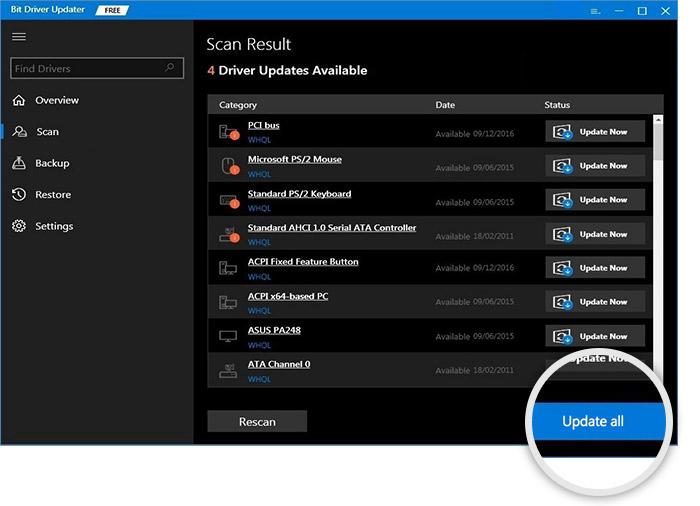
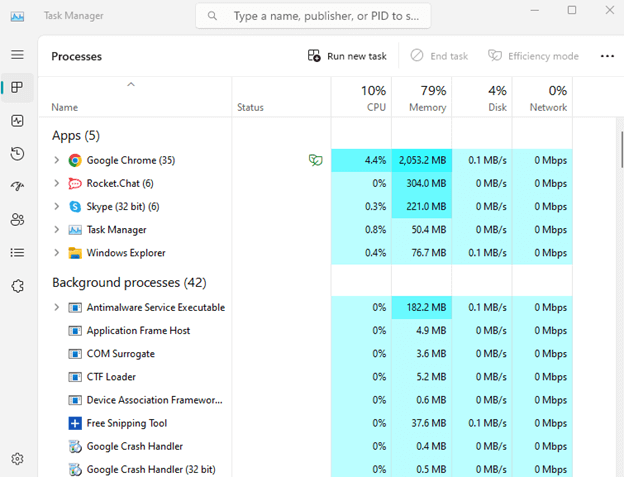
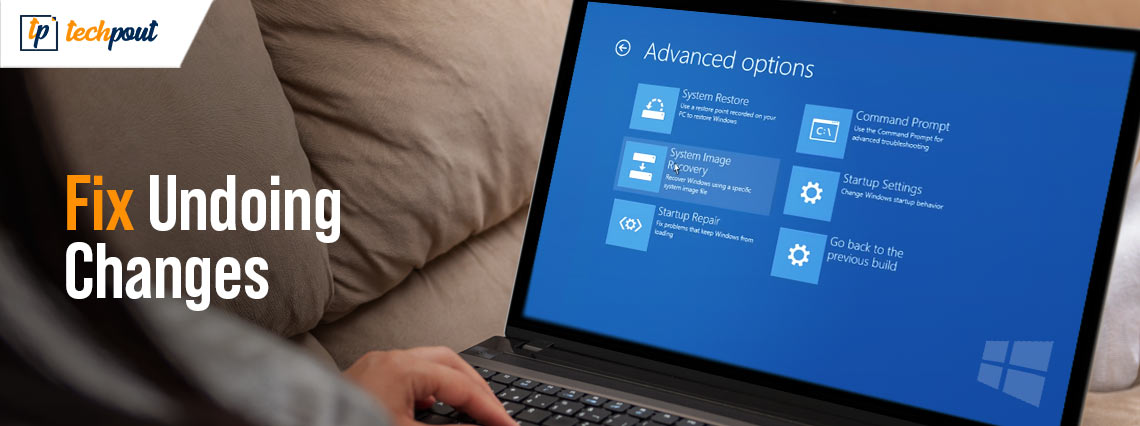
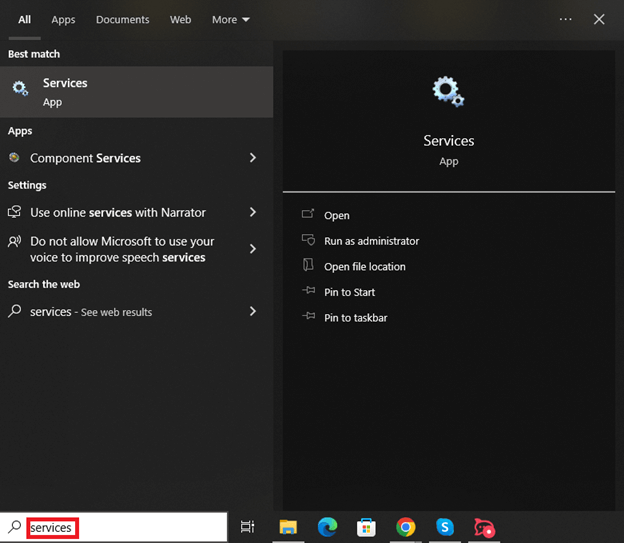
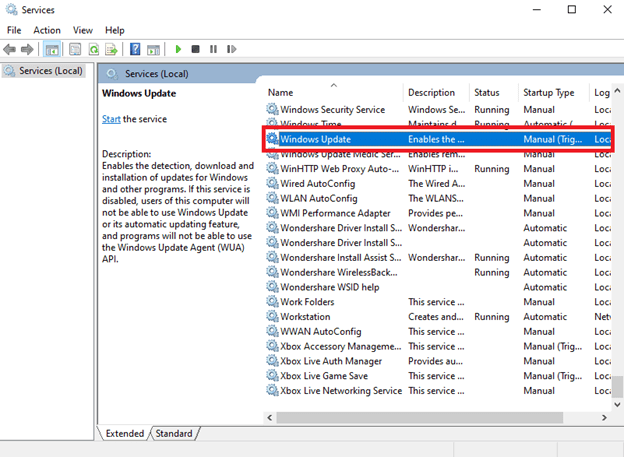
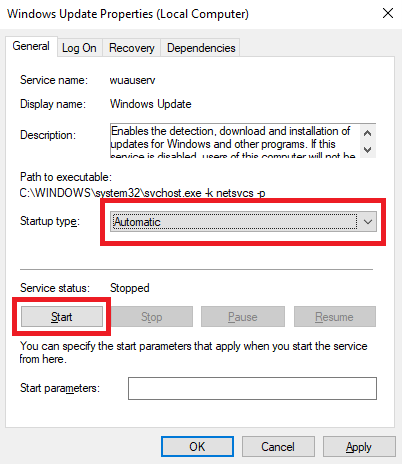
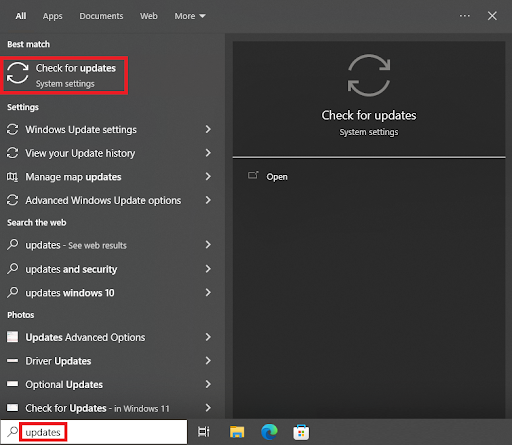
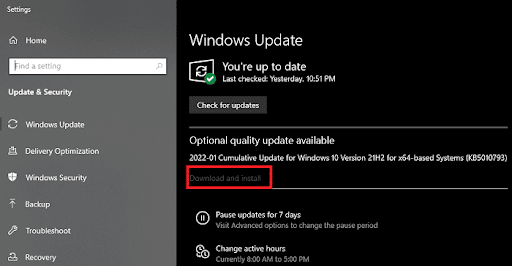
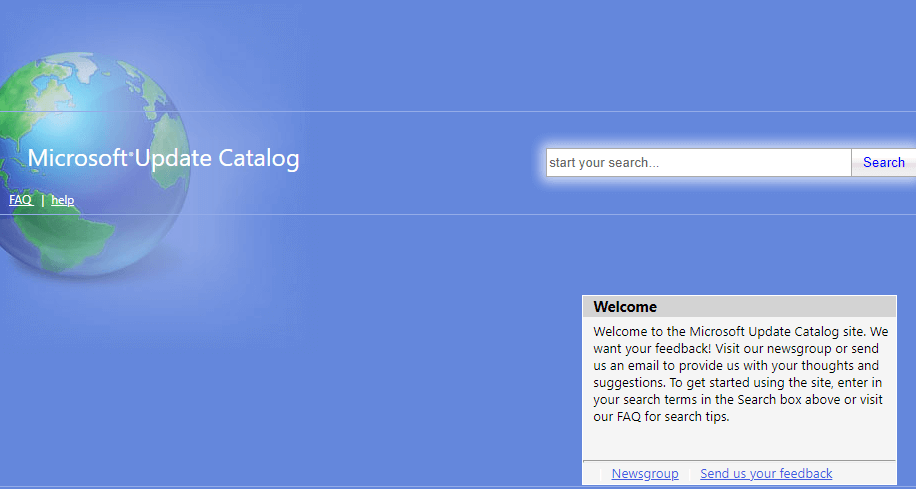
- Update your device and apps as soon as you receive a notification to do so.
- Set updates to be done automatically, preferably at night.
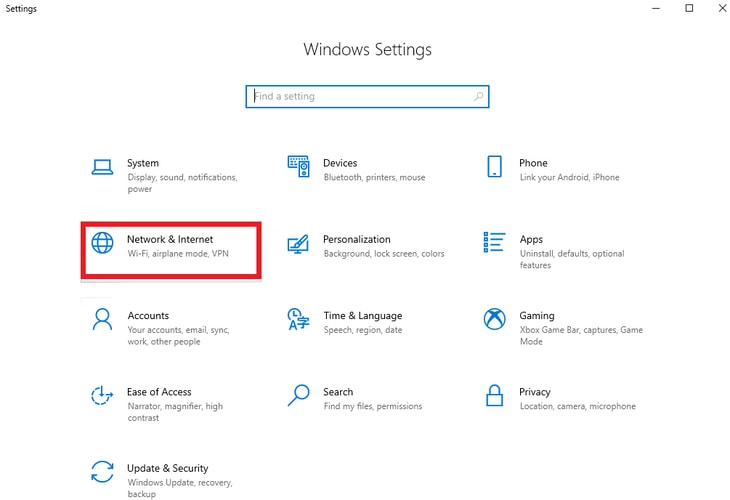
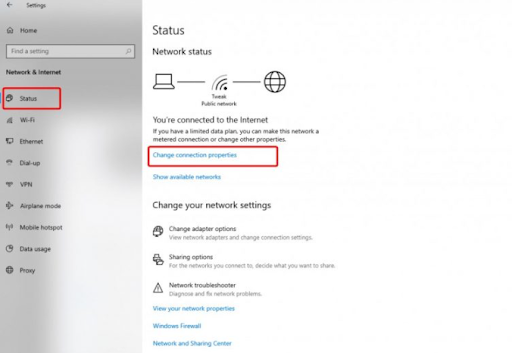
- Install a VPN to ensure that all your data travels through the digital space safely. Thanks to tools like Atlas VPN, all internet traffic will be encrypted. Thus, this action might prevent hackers from eavesdropping on it, even if vulnerabilities would allow them to.
- Get robust antivirus tools. These programs are crucial as they check and maintain the security of your device.