Digital attacks are getting more and more common by the day. Digital threats from hackers, ransomware developers, and other security meddlers are becoming a thing to worry about for all. Thankfully, cybersecurity and its practices are there to protect you from such threats. There are multiple cybersecurity measures that can help you protect your business and personal data from being leaked, extorted for, corrupted, or rendered vulnerable in other ways.
Multiple cybersecurity measures are there to help you, but the domain is so wide that there is so much to discover. Moreover, the complexity of cybersecurity practices also makes it difficult for individuals and businesses to utilize them. But, there are experts who can be of great help when it comes to cybersecurity. Faiq Farooq, a lead cybersecurity consultant, is one of them.

Faiq Farooq is a celebrated name in the cybersecurity industry. He, having a CISSP(Certified Information System Security Professional), is a diligent professional with many feathers in his cap when it comes to assessing and protecting his clients from security threats, designing mitigation strategies, and bringing appropriate security measures into force.
Having contributed 8 valuable years to the world of cybersecurity, Faiq Farooq has earned a reputation and many certifications in his name.
It all began when he started his professional career at Al Yousuf LLC, UAE as a Technical Engineer. In this role, he gained the skills and knowledge required to revolutionize the cybersecurity industry. His responsibilities may have been limited, but he outshined in all aspects. He was rewarded with the task of creating a stable network environment that connects all peers to a single channel, which he executed impeccably.
Presently, Faiq has been working as a Lead Cybersecurity Consultant at Intech Process Automation. For the past two years, this role required him to lead the entire cybersecurity team and guide them toward self-curated projects, procedures, and more. One of the most crucial aspects of his role was to implement the Mcafee EPO and Symantec-centralized solutions that could meet the requirements of specific vendors. He also designed and monitored the Claroty CTD (Continuous threat detection) system in the OT environment. Being the sole individual responsible for the Business Continuity Plan (BCP), Faiq also underwent fruitful business impact analysis (BIA) using the MAO, RTO, RPO, and other metrics. Moreover, the role also motivated him to set up backup solutions in a multi-tier vendor system.
Prior to this, Faiq was a part of PEPSI Co. and PKLI & Research Centre (before PepsiCo.) as a System Administrator. Here, he had been credited with the utmost responsibility for designing and implementing test specifications for different kinds of cybersecurity H/W & S/W systems. Moreover, he also handled the operational impact analysis for the company. He also installed multiple servers that can meet the requirements of the business and keep it running uninterruptedly. He was quite impeccable in setting up and maintaining the viability of firewall systems as well.
With the organizations, he has worked as a CCNA (Cisco Certified Network Associate) and grew to be the cybersecurity lead, CISM (Certified Information Security Manager), and PECB Certified ISO/IEC 27005 Lead Risk Manager. In the positions, he designed multiple cybersecurity measures and executed them for different clients and in-house requirements. As he was also a senior resource, he was also responsible for the training of the new joiners.
Also, he was rewarded with the crucial responsibility of backing up and protecting the existing cybersecurity measures that he completed impeccably.
In his eight years of experience after completing a Bachelor of Commerce from Punjab University Lahore and a Master of Science from the University of Sargodha, he has served in some of the most reputable organizations, such as Pepsico., Intech Process Automation, etc., as a leader in various projects, which is a testament to his outstanding abilities.
While contributing to challenging projects in his career, as an ISA/IEC 62443 Cybersecurity Certified Fundamentals Specialist, he honed many useful skills, such as Vulnerability Assessment, Claroty Secure Remote Access, Incident Management, Business Impact Analysis (BIA), Business Continuity Plan (BCP), FortiGate Firewalls, and more.
To learn about Faiq Farooq, a CEH (Certified Ethical Hacker) and Claroty Support Engineer CSE 501, at a more professional and personal level, we engaged in tête-à-tête with him. Here are a few excerpts from the same.
1. What inspired you to pursue a career in cybersecurity, and how did you become a consultant in this field?
Answer: I’ve always been fascinated by technology and driven to have a positive influence online. I was motivated to seek a career in Information Technology, by this passion and my thorough knowledge of its crucial necessity. My path toward cybersecurity started with a strong academic background. My Master’s degree in Science & Information Technology gave me a deep understanding of technology as well as its challenges. As I learned more about the topic, I understood how important it is to protect digital assets and data.
2. Can you share some examples of successful cyber security consulting projects or initiatives that you’ve been involved in and the impact they had on the organizations you served?
Answer: In One Project, where I am currently working is for one of the Major Oil and gas organizations in Oman and we are implementing CSMS (Cybersecurity Management System) for them. This project is about studying regulatory and organizational requirements, finding the standard to comply with government regulations, drafting comprehensive CSMS (cyber security management system), detailed gap and vulnerability assessment, risk assessment using ISA 62443 standard, controls implementation to overcome non-conformities, etc. This project is still ongoing, and we have already achieved multiple milestones.
3. As a Lead Cyber Security Consultant, what is your approach to identifying and mitigating cyber risks for your clients?
Answer: As a Lead Cyber Security Consultant, I take a thorough, proactive approach to identifying and mitigating cyber risks for customers in order to effectively safeguard their digital infrastructure and assets. It includes several crucial stages.
- Assessment and Understanding
- Threat and Vulnerability Analysis
- Risk Prioritization
- Security Frameworks and Standards
- Implementation and Integration
- Security Awareness Training
Also Read: Cyber Security Threats to Small Businesses
4. In your experience, what are the most pressing cybersecurity concerns facing businesses and organizations today?
Answer: According to my observations, businesses and organizations are currently most concerned about a number of urgent cybersecurity issues. These difficulties are a reflection of the dynamic threat environment and the demand for strong security measures. The following are the top issues and their mitigation.
- Ransomware Attacks Prevention and Mitigation (Keep up-to-date, secure backups of important data stored independently from the network, Train employees to recognize phishing attempts and malicious attachments)
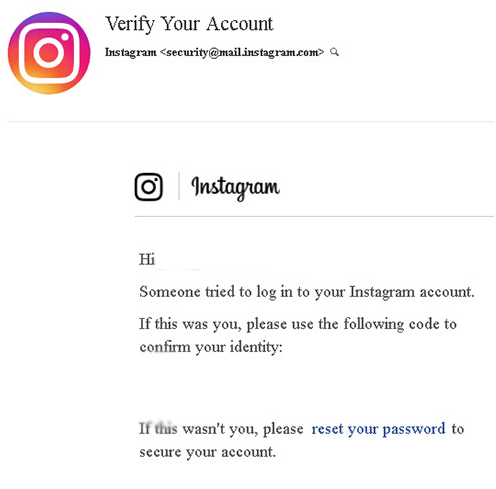
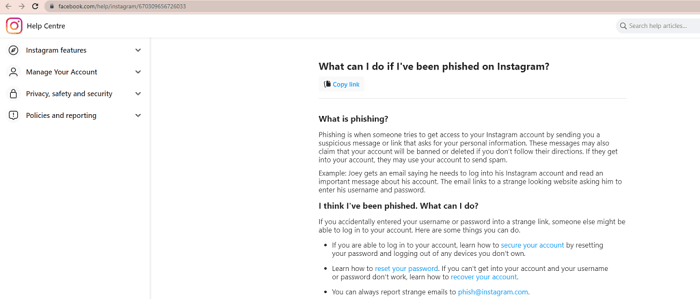
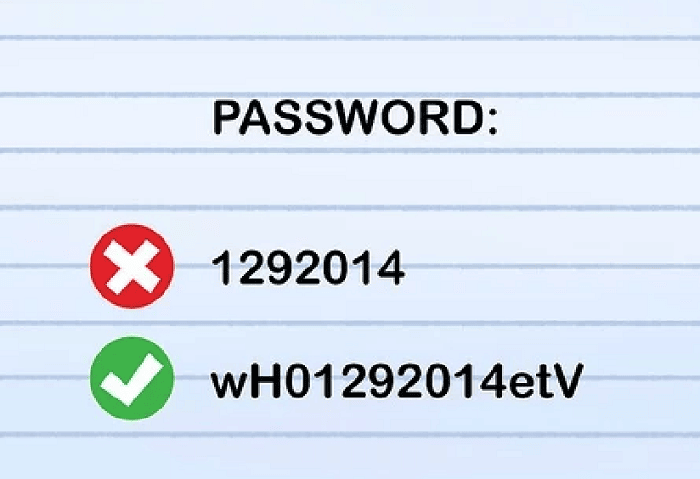
- Phishing and Social Engineering Prevention and Mitigation (Comprehensive cybersecurity awareness training is essential to help individuals recognize and avoid phishing emails and social engineering tactics, Implement email filtering solutions to identify and block phishing emails before they reach users’ inboxes, Enable MFA (Multi-Factor Authentication) on accounts to add an extra layer of security, even if login credentials are compromised)
- Insider Threats Prevention and Mitigation (Implement robust cybersecurity awareness training programs to educate employees about security risks, phishing, and best practices, Enforce the principle of least privilege, ensuring that employees have access only to what is necessary for their job roles, Employ security tools and practices to monitor user activities and access, allowing for early detection of suspicious or unauthorized behavior.)
- Zero-Day Vulnerabilities Prevention and Mitigation (Even though a zero-day vulnerability has no official patch, stay informed about vendor updates and apply patches as soon as they are released, If a system is compromised, isolate it from the network to prevent further spread and damage)
5. Can you share examples of how you’ve helped organizations improve their cybersecurity posture and prevent or respond to cyber incidents?
Answer: I’ve had the honor of working for different firms to improve their cybersecurity posture and successfully stop or respond to cyber incidents. Here are a few noteworthy instances
- Vulnerability Remediation Strategy (We carried out a thorough vulnerability analysis for a healthcare provider who must adhere to HIPAA compliance rules. Several significant vulnerabilities in their systems were discovered throughout the examination. We prioritized and remedied these weaknesses in close collaboration with different Teams, lowering the likelihood of data breaches and compliance infractions.
- Regulatory Compliance Readiness (In One Project, where I am currently working is for one of the Major Oil & Gas organizations in Oman and we are implementing CSMS (Cybersecurity Management System ) for them. This project is about studying regulatory and organizational requirements, finding the standard to comply with government’s regulations, drafting comprehensive CSMS (cyber security management system), detailed gap and vulnerability assessment, risk assessment using ISA 62443 standard, controls implementation to overcome non-conformities, etc)
6. What advice would you give to individuals aspiring to pursue a career in cybersecurity and eventually become consultants in the field?
Answer: Cybersecurity It’s a challenging and lucrative industry, but it demands commitment, ongoing education, and a calculated approach. Attain a degree in Information Technology, Gain Practical Experience, Pursue Certifications, Specialize in an Area of Interest, Develop Strong Communication Skills, and Stay Informed and Curious.
Also Read: Cloud Security Best Practices: Protecting Your Business in the Digital Era
7. Can you share any specific examples of your contributions to thought leadership or research in the field of cybersecurity?
Answer: I’m honored to have made some contributions to cybersecurity research and thought leadership. My desire to remain at the forefront of the field and impart knowledge to advance the larger community has motivated these efforts.
Mentorship and Education (I regularly mentor newcomers and my juniors to the subject of cybersecurity and have created my own learning materials and learning methodology, such as study guides, to help those aiming to earn pertinent certifications. I’m committed to passing on my expertise, and knowledge and assisting others in succeeding. I also take part in providing various knowledge-sharing sessions with practical demonstrations relating to cybersecurity as the Lead Cybersecurity Consultant in my Organization )
That was all for the day. We thoroughly enjoyed speaking with Faiq Farooq and wish him all the best in his future endeavors. Moreover, we look forward to interacting with more such renowned personalities, making the cyber world a safer space for one and all.