Here Are Some Tips To Help You Overcome Online Scams
Given the amount of malware on the network, and hacking, you can confirm the fact that the Internet is not all that secure. The influx of devices ranging from tablets and smartphones to Internet tools has significantly exposed us to many dangers.
However, there is another side to the coin – the many benefits associated with it that will make you long for it. The only trick here is for you to train for cyber-security measures so you can win the trap and stay safe while surfing.
Maybe that’s not a new trick for you; however, generating strong and complicated passwords for your accounts is considered the best way to stay secure. It gives you complete control over your financial and private data. Attributing to the current situation of a wide corporation scam involving the misuse of a database where millions of passwords are revealed, you cannot avoid this advice.
Hackers have easier access to personal data, especially when passwords are reused multiple times. They will use the information discovered after the attack to gain access to your remaining accounts. In this case, it is recommended to use a password manager that will allow you to keep and generate more complex passwords for entire accounts.
The late internet offers countless internet sharing opportunities to everyone. You only need to be sure of what you are sharing, especially if it includes your details. This could be the best chance for anyone to access your login information. While the internet is the best opportunity for us to make our life dreams come true, our security is equally important. By following the above and other tips not mentioned here, you can be sure that you will get the most out of your online experience.
Security When Using Public Computers
Internet cafes, also called cyber cafes or net cafes, are places that offer computers with some form of network access for public use, usually for a fee. You can find computers on the Internet for public use in copy centers, hotels, cruise ships, airports, or anywhere you can access the Internet. They can also provide hardware that allows you to print and scan documents. Internet cafes are especially useful for travelers who do not carry computers with them. They are common in many countries, and using their services is often cheap if you only check emails, share digital photos. Computers in Internet cafes are public systems and as such are less secure than those you use at home or in the office. Take extra precautions when using them, especially when it comes to sensitive information.
Bring a USB flash drive with portable programs, settings, and documents. The good thing about this method is that you can have all your data with you, but when you disconnect the USB flash drive, none of your data remains on your computer. Make sure that antispyware and antivirus software is installed on the USB flash drive. Please note, however, that some locations may not allow you to use a personal USB device on their systems for security reasons.
Remember login credentials for any system you may need to access, such as your email account. Look for a message from the system asking if you are accessing from a public or private computer and be sure to select “public”. This allows personal information not to be stored on your computer after you finish. When you’re done with the session you’re signed in to, such as email, always sign out when you’re done so that users who come after you don’t accidentally gain access to your account. Clear your web browser history, temporary files, and cookies when you’re done. It is best to avoid logging in to sites where you have sensitive information, such as your bank account, if at all possible.
How To Protect Your Information On The Internet
Before registering on a social network, we need to read the privacy settings. The problem arises in cases where personal data is left, exchanged, collected, or disseminated further. All of the above may compromise data privacy. Therefore, when appropriate, we may use a pseudonym that does not disclose our personal information. Privacy can be linked-to anonymity because anonymity is used as an instrument to exercise freedom or protect a person’s privacy. Check the potential risk to your own privacy when using the Internet and providing personal information. It is common in most cases to require registration during which the user must submit their personal information, most often an email address, name, and surname. Through the Privacy Calculator application, we can educate ourselves, and this application will encourage us to think about security and privacy issues on the Internet. Young people can hardly imagine life without the daily use of social networks. The rules of good behavior on networks adapt to new technologies, but the old rule, which also applies in real life, applies at every opportunity: “Let’s treat others the way we want others to treat us.”
Password Manager Application – Powerful Password Generation
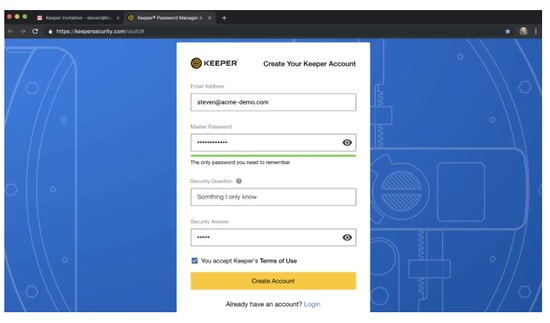
To avoid confusion with dozens and hundreds of passwords and save time on authorizing and entering personal information on various websites, it is convenient to use a password manager. These kinds of security tools, for example, Keeper Password Manager can upgrade your security significantly. Keeper comes with a variety of different features that allow you to have a more secure chat between your employees, protection from the dark web, and a lot more, that you can find out here. When working with such programs, you will need to remember one master password, and everything else will be under reliable cryptographic protection and always at hand. For security reasons, it is recommended that you come up with an original password with each new registration, because otherwise, if an attacker gains illegal access to one account, he will be able to easily break into others.

Remembering a lot of different usernames and passwords is difficult, writing to notepad is not secure, so the best option for unloading memory is to use special programs to save passwords. Download this app. In addition, they have several basic functions. Some password managers can quickly create a password, which uses a unique combination of letters, characters, and numbers. Some of the advantages are also the automatic filling of files and queries, simple user interface, the possibility of using two-factor authentication, and device synchronization.






2 Comments
[…] that is offered by the Bullguard firewall method is the installing of the current protection https://www.techpout.com/cybersecurity-data-protection/ feature. With this feature, it detects any efforts at hacking into your computer and then blocks […]
[…] https://www.techpout.com/cybersecurity-data-protection/ is a leading security answer provider known for its malware protection and firewalls. The fire wall […]